Impact on Marketing
Spambots aren’t just causing havoc for cybersecurity professionals but also making it more difficult for institutions to recruit new students effectively.
“They cause a big headache and a lot of wasted time for admissions officials,” Merrill said.
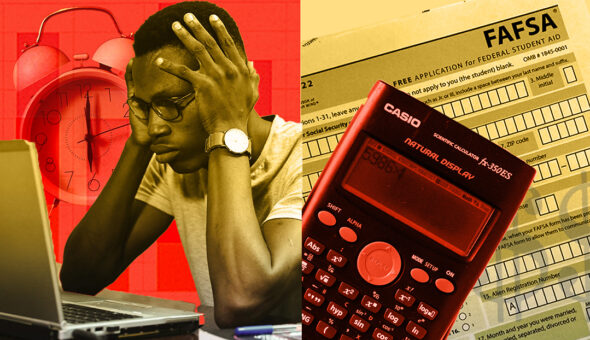
This comes at a point when enrollment across the nation is faltering, down 1.23 million undergraduates for the fall of 2022 compared to pre-pandemic numbers in the fall of 2019, according to the National Student Clearinghouse Research Center.
“I would imagine it inflates marketing spend per student—meaning the farther down the funnel, the more time/money is spent on a student,” observed Chris Huebner, Volt contributor and director of activation at the higher education marketing agency SimpsonScarborough.
That impact isn’t trivial, as it costs an average of $2,795 for four-year private schools and $494 for public schools to recruit a traditional student, according to a 2022 report from the higher education enrollment firm RNL.
Rose explained that the goal of advertising platforms such as Google Ads is to show users the most relevant advertisements. One way of doing so is the collection of data through HTTP cookies.
“When you have bots doing all of this automated web browsing, searching and going to university websites, you begin to skew the profiles. They tend to think that a bot or IP address is interested in enrolling in school,” he explained. “Universities are very competitive because they need to fund their programs. They’re paying high dollar for these advertisements. Every single time they’re being shown or clicked on by a bot, that’s essentially money that’s, not by the fault of the ad provider, being taken illegitimately from the university.”
Sussman added that it becomes more difficult for marketers to gain accurate demographics any time fraudulent accounts are made.
“If all the sudden your registration increases by factors of tens or hundreds, you’re either doing something right or you’re looking at a bot attack,” she said.
Jamie Hunt, vice president for university communications at Old Dominion University and Volt Insights contributor, agreed with Sussman, “Bots can interfere with marketing by distorting campaign results, which makes it challenging to measure campaign performance and optimize future campaigns.”
Malicious, and even unsuspicious, bot activity reduces the effectiveness of online marketing, Holtzman noted.
“It can deplete ad budgets, distracting attention away from intended audiences and/or making way for competitors to secure prime placements; it can flood systems with fake data and requests, preventing legitimate requests from being received and diminishing conversion rates; and it skews performance metrics, leading to a lack of understanding of genuine interest, campaign effectiveness and high-priority opportunities,” she said.